Why Regulatory Compliance Is the Backbone of Security Leadership
In the Philippine operating environment, security leadership is not defined by the number of guards deployed, the sophistication of surveillance systems, or the speed of incident response. Those are capabilities. Leadership is the governance that makes those capabilities defensible to the Board, to regulators, to clients, and, when necessary, to courts and investigators.
That is why regulatory compliance is not a “support function.” It is the backbone of security leadership.
Compliance is where strategy meets enforceable reality. It forces clarity on questions executives cannot afford to answer loosely: What standards are we committing to? Who is accountable? What is the organization’s risk appetite? What evidence proves it? In the Philippines where enforcement is multi-agency, renewal-driven, and highly document-centric compliance becomes the operating system that determines whether security programs are credible or merely performative.
This matters because the harsh truth is consistent across publicly reported incidents: after a crisis, organizations are judged less by what they intended and more by what they can document, govern, and prove.
The problem executives keep inheriting
Many organizations still treat compliance as an annual ritual: business permit season, inspection season, audit season. That approach creates three executive blind spots.
First, it misunderstands what regulators and courts evaluate. In high-risk incidents, the question is rarely “Did you have good people?” It is “Did you have governance controls policies, approvals, inspections, training records, licensure validation, and oversight—that match your risk profile?”
Second, it fragments accountability. Safety may sit with Operations, Fire with Facilities, OSH with HR, data privacy with IT/Legal, private security licensure with Procurement, and crisis management with Corporate Affairs. Fragmentation produces gaps, and gaps produce exposure.
Third, it hides risk in vendor relationships. Many Philippine organizations outsource core security functions to private security agencies. But outsourcing operations does not outsource accountability especially when incidents trigger contractual claims, administrative sanctions, or litigation, and the client’s due diligence becomes part of the record. The Supreme Court has explicitly criticized “total reliance” on a security agency’s paperwork when a client fails to verify qualifications and required documentation it contracted for.
A security leader who cannot speak the language of compliance is not managing security risk; they are managing security activity.
Philippine regulatory reality and what it means for leaders
Security compliance in the Philippines is not one law or one regulator. It is an ecosystem. The strategic implication is direct: security governance must be designed to survive overlapping jurisdictions, and the renewal and inspection mechanisms that make enforcement real.
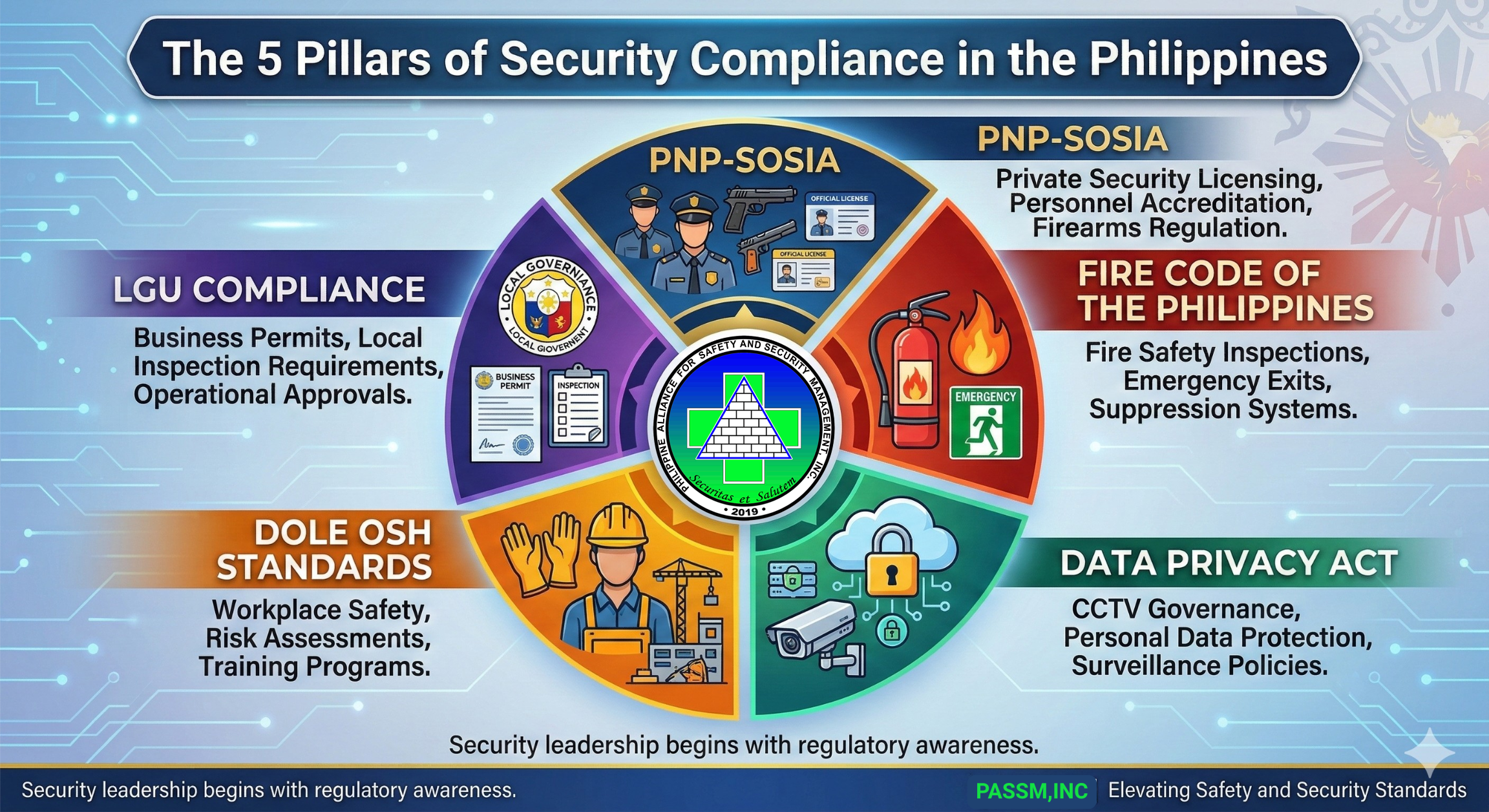
Private security regulation and the PNP-SOSIA compliance baseline
Private security is regulated through the Philippine National Police ecosystem, particularly its Civil Security Group, with licensure and oversight functions associated with SOSIA.
The legal framework was strengthened through Republic Act No. 11917, which defines two compliance anchors executives should understand:
- License to Exercise Security Profession (LESP) – a permit issued by the Chief PNP (or authorized representative) recognizing a person as qualified to perform duties as a security professional or training personnel.
- License to Operate (LTO) – a permit authorizing a person or juridical entity to establish/manage a private security agency or company guard force (and related services), subject to requirements under implementing rules.
RA 11917 also places meaningful penalties on operating without a valid LTO and on deployment of unlicensed security personnel, and it explicitly provides that if the offender is a juridical entity, penalties may attach to officers who participated in the decision leading to the violation. This is an executive-level governance issue, not a back-office concern.
Operationally, what does the compliance baseline look like in practice? PNP-issued requirements have historically been documentation-heavy. For example, a PNP memorandum circular updating LTO documentary requirements enumerates items such as inspection reports, critically for Philippine operational realities local requirements like a Mayor’s permit for the principal/branch office, among many others.
This explains a recurring Philippine compliance gap: private security firms (and sometimes their clients) can be operationally present while administratively fragile licenses nearing expiry, incomplete clearances, outdated guard records, or weak evidence of supervision and qualification.
The enforcement reality is not theoretical. Publicly reported actions show the PNP conducting compliance efforts that include cease-to-operate orders and firearms accounting. In one government report, the PNP confiscated over 1,000 firearms from dozens of private security agencies served cease-to-operate orders and cited failure to renew licenses that led to revocations. Another report notes PNP-directed crackdowns on unauthorized private security personnel, highlighting requirements such as Special Duty Detail Orders (SDDO) and authorities to deploy protective agents.
For security directors and corporate executives, the strategic takeaway is simple: vendor selection is governance; licensure validation is risk control. If your contracted security provider is administratively non-compliant, your organization inherits operational disruption risk and potentially reputational and legal exposure at the worst possible time.
Fire Code enforcement and the “license to operate” of facilities
The Fire Code is explicit that enforcement is administered by the Bureau of Fire Protection under DILG supervision. It provides administrative enforcement mechanisms that matter to executives: the BFP may impose administrative fines, stop operations, or order closure of buildings and facilities that do not comply with Fire Code requirements and the payment of fines does not absolve the violator from correcting deficiencies.
In executive terms: fire compliance is a business continuity control. If a site can be closed for non-compliance, then compliance is not a “Facilities issue.” It is a business risk issue.
There is also a governance dimension in how Fire Code compliance interacts with LGU permitting. The Philippine business permitting environment operationalizes compliance through renewals. A joint government circular on business permitting standards states that upon renewal, clearances and certificates required by national laws and regulatory bodies explicitly including FSIC must be complied with, and that regulatory bodies may provide LGUs lists of non-complying establishments as basis for non-renewal.
OSH as an executive accountability system, not a safety program
Republic Act No. 11058, the OSH law, is often discussed as an HR or Safety function. Executives should read it differently. RA 11058 embeds governance through three mechanisms that directly affect security leadership.
First, it mandates covered workplaces to maintain an OSH program inclusive of emergency preparedness and response planning, incident reporting, and other core controls.
Second, it imposes joint and solidary liability on the employer, project owner, general contractor, and other responsible parties for compliance, an explicit accountability model designed to prevent blame-shifting in complex operational setups.
Third, it creates enforcement teeth: the Secretary of Labor (through Department of Labor and Employment) has visitorial powers to inspect, enter workplaces, examine records, and order stoppage of work when noncompliance poses grave and imminent danger. It also authorizes administrative fines up to ₱100,000 per day until violations are corrected for willful failure/refusal to comply with OSH standards or compliance orders.
Security leaders should integrate OSH requirements because many security decisions crowd density, emergency egress governance, hazardous area controls, contractor management sit directly on OSH exposure.
Data Privacy and the compliance consequences of “security technology”
Security programs increasingly rely on personal data: CCTV footage, access control logs, visitor management records, and incident documentation. Under the Data Privacy Act, the Principle of Accountability states that a personal information controller remains responsible for personal information under its control or custody, including data transferred to third parties for processing, and must use contractual or other reasonable means to ensure comparable protection.
In security leadership terms, that means: outsourcing your CCTV monitoring or using a third-party security platform does not outsource accountability.
The National Privacy Commission reinforced this reality through NPC Circular No. 2024-02, which provides an updated policy framework on CCTV systems and emphasizes that CCTV systems process personal data, requiring safeguards that align with privacy principles and data subject rights. The circular describes core governance expectations—visibility of CCTV notices, lawful basis determination, proportionality/data minimization, and policies including privacy impact assessments and breach procedures.
For executives, the message is strategic: technology modernization without privacy governance creates regulatory risk. The same tool intended to strengthen security can become a compliance liability if governance is absent.
Publicly reported cases and what they teach leaders
Philippine incidents repeatedly show that compliance failures are rarely “one missing permit.” They are systemic governance failures where oversight, documentation, enforcement, and decision-making collapse into a single catastrophic outcome.
Kentex factory fire and the LGU–FSIC governance gap
In a Supreme Court decision discussing the Kentex Manufacturing Corporation fire in Valenzuela City, the Court recounts findings from an inter-agency investigation: the fire led to the death of 74 individuals and injuries to others, and investigators concluded many casualties died in areas indicating lack of exit points.
What is most instructive for compliance leadership is the interaction of national standards and local enforcement. The same decision notes that business permits were issued in years when the facility lacked a Fire Safety Inspection Certificate (FSIC), and that an FSIC issued in 2012 was valid for one year with no subsequent renewals, yet business permits were later issued despite the lack of FSIC.
This is not merely a fire safety story. It is a governance story:
- Regulatory requirements can exist, but if permitting workflows allow exceptions or if post-audit practices are weak risk accumulates invisibly.
- Compliance cannot be delegated entirely to government enforcement; organizations must internalize the compliance standard as a self-governance system.
For executives, the Kentex case demonstrates why compliance must be treated as a risk control owned by leadership, not simply “what the LGU requires this year.”
Ozone Disco fire and the cost of ignoring compliance as capacity planning
The Ozone fire (publicly reported as one of the deadliest nightclub fires) remains a defining Philippine example of how occupancy risk and building code compliance intersect with governance failures.
An Associated Press report on the aftermath notes that about 400 people were packed in the venue when the fire broke out, and many could not escape because an emergency exit was blocked by a new building next door. The same report notes convictions connected to approving a building permit despite non-compliance with building code requirements.
The executive lesson is not “inspect exits.” The executive lesson is:
- Capacity planning is compliance. Overcrowding is not merely crowd behavior; it is a governance decision about allowed capacity, ticketing, and enforcement of entry controls.
- Permitting is not protection. Permits can exist while conditions degrade over time through renovations, space encroachments, and operational changes.
Ultra stampede and why event compliance is a governance discipline
If you work in major events, compliance is not primarily about paperwork. It is about decision architecture.
A Supreme Court decision arising from the PhilSports Arena incident describes how crowds gathered for days and surged after gates opened; the stampede claimed 71 lives (69 women) and left hundreds wounded, prompting emergency support and cancellation of the program episode. The decision also describes immediate creation of an inter-agency fact-finding effort under DILG and the subsequent DOJ evaluation and investigative actions.
The governance lesson is this: large-scale public events are regulated environments. When crowd volume, ticket allocation, entry timing, and communication to participants are mismanaged, the result is not only operational failure it becomes a regulatory and legal matter, involving investigations, accountability, and organizational scrutiny.
For security leaders advising event organizers and corporate sponsors, compliance is the framework that turns decision-making into auditable controls.
Strategic recommendations executives can implement now
Security leaders should treat compliance as a leadership system with four integrated components: risk scoring, governance structure, executive reporting, and decision discipline.
A practical compliance risk matrix for security leadership
Use a standard 5×5 likelihood–impact matrix, but define “impact” in executive terms:
- Regulatory impact: closure orders, permit non-renewal, sanctions
- Operational impact: disruption, site shutdown, inability to deploy licensed personnel
- Legal impact: contractual claims, litigation exposure, officer liability triggers
- Reputational impact: stakeholder trust, investor/client consequences
- Financial impact: direct loss plus remediation costs
Then classify compliance risks into categories such as:
- Licensure risks (PNP-related LTO/LESP validity, deployment authority constraints)
- Facility risks (Fire Code compliance, FSIC-linked permit renewal exposure)
- Workplace risks (OSH program gaps, stoppage power exposure, daily fines)
- Data risks (CCTV governance, third-party accountability, privacy safeguards)
The objective is not to “rate everything.” The objective is to create a single page that helps executives decide what gets attention first.
Governance structure that matches Philippine enforcement realities
A common failure in Philippine organizations is assuming “Compliance” is one department. Instead, design governance based on how enforcement actually happens:
- Board / Executive Committee: sets risk appetite; requires quarterly compliance risk reporting.
- Risk & Compliance Council (management-level): owns jurisdiction mapping (PNP/LGU/BFP/DOLE/NPC) and approves remediation priorities.
- Security Governance Lead (Security Director or equivalent): integrates vendor licensing, incident governance, and regulatory readiness.
- Facilities / OSH / HR / IT-Legal: each owns domain compliance controls with documented KPIs and evidence packs.
The Kentex decision is an example of why this governance matters: business permits were issued despite FSIC gaps showing that reliance on external enforcement alone is not a risk strategy.
Executive reporting format that survives audits and crises
An executive compliance dashboard should be decision-oriented, not operational noise. Minimum contents:
- Top 10 compliance risks with trend direction (improving/stable/worsening)
- Licensure status: private security partner LTO/LESP validation status and renewal calendar
- Permit readiness: FSIC status and permit renewal dependencies, including LGU timeline constraints
- OSH compliance posture: audit findings, imminent danger flags, corrective actions, and inspection readiness
- Privacy posture for security tech: CCTV policy status, notices, PIAs, access controls, vendor agreements
- Incident & enforcement log: regulator interactions, inspection outcomes, closure threats, show-cause notices
The key is to operationalize a truth executives understand: if it is not reportable, it is not governable.
Decision-making checklist for leaders approving security programs and vendors
Before approving a security contract, technology deployment, or event security plan, require leadership teams to answer five questions:
- What regulation(s) govern this activity and which agency enforces them in practice?
- What evidence proves compliance today (licenses, certificates, audit trails, policies)?
- What is the failure mode if compliance lapses (closure, stoppage, fines, litigation)?
- What is the vendor accountability model and what due diligence can we prove?
- Who is the accountable executive if the regulator, Board, or court asks “who owns this”?
The Supreme Court’s reasoning in the university shooting case is a cautionary governance marker: when an organization contracts for qualification requirements but fails to verify key records, “total reliance” becomes negligence.
Closing: compliance-led security is the standard of serious organizations
The organizations that lead in security are not those with the loudest presence or the most impressive hardware. They are the ones whose security decisions are anchored in governance where compliance is integrated into procurement, operations, technology, and leadership accountability.
The Philippine context makes this non-negotiable. PNP licensing regimes can disrupt operations when vendors and protective agents are unlicensed or unauthorized. Fire Code enforcement can escalate into stoppage or closure, and FSIC-linked workflows can affect permit renewals. DOLE oversight carries inspection and stoppage powers and daily administrative fines for willful noncompliance. Security technology decisions now sit within privacy regulation, with the NPC explicitly framing CCTV governance around transparency, proportionality, safeguards, and accountability.
PASSMI positions security leadership where it belongs: as a standards-setting profession grounded in governance, compliance, and risk thinking not as a purely operational function. Leaders who want to elevate their organizations should treat structured professional development as a governance investment. The CSSMP pathway is designed to professionalize decision-making across regulatory compliance, corporate governance, risk management, and modern security leadership so that compliance becomes not an annual scramble, but a permanent capability.
If you are a Security Director, corporate executive, risk manager, compliance officer, event organizer, or security agency owner, the call is clear: elevate standards through structured certification and training because in the Philippines, compliance is not paperwork. It is leadership.
Elevate Your Security Leadership.
If this article challenged the way you think about safety and security, the next step is structured professional development.
The Certified Security & Safety Management Professional (CSSMP) program is designed for executives, managers, and agency leaders who want to move beyond operational supervision and into risk governance, compliance integration, and strategic leadership.
This is not guard-level training.
This is executive-level elevation.
Leaders define industries.

